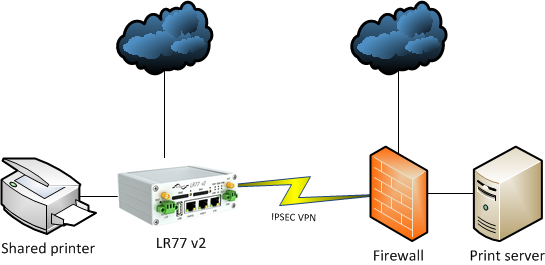
I am currently evaluating the Conel LR77 v2 router for my customer, and so far I am very impressed. This is the first mobile router I have seen for LTE (4G) that has support for IPSEC VPN.
This is description of a problem i have found then accessing devices behind the router over a VPN connection.
It all started when I tried to send a printout to a IP printer behind the LR77 router and it failed. I also tried to access the printers web interface, but that also failed. The printer was however reachable using ICMP ping.
First I suspected that there where some general errors initiating TCP sessions from the other side of the VPN tunnel, but that was not the problem. There is a bug in the iptables configuration in the router.
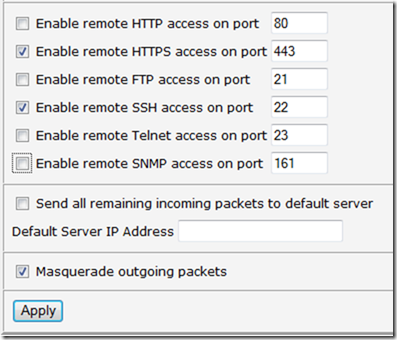
There is a function in the router configuration to allow or disallow remote management:
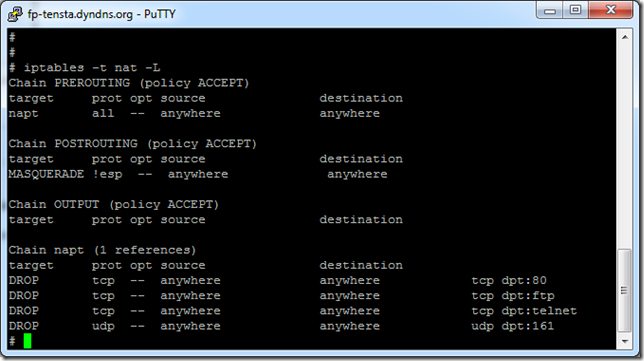
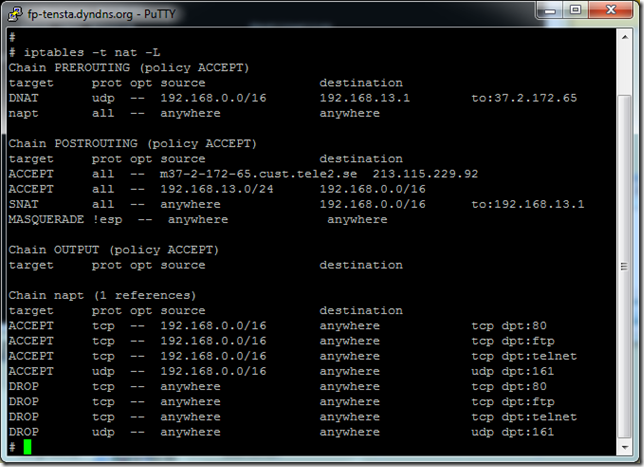
I had disabled all unencrypted management functions from the WAN site of the router, and this option will result in the following IPTABLES configuration:
The last tree lines are the “removed checkboxes” in the LAN setup page in the web GUI. The problem is that these lines do not only block access on the WAN interface, they also drop traffic from the IPSEC tunnel to the LAN interface on the specified ports. And UDP port 161 is used by TCP/IP printing.
Well, that’s about the problem. Is there a workaround? One option would be to enable all remote management ports again, but that did not seem very pleasing.
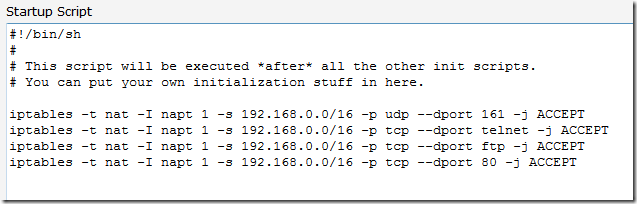
Luckily the Conel router gives you a lot of power. There is an option to add scripts to run whenever the router boot up.
The following script will add rows to the napt chain to allow traffic from all my local networks, I have a number of 192.168.x.0/24 networks.
The result looks like this:
I do not claim to be a iptables expert, so I give you no warranty what so ever on this solution. All I know is that this gives you the possibility to access your stuff on the LAN. Do not blame me if this opens up some other security problems.
5 svar på ”Bug in Conel LR77 v2 router using IPSEC”
Good information. Thank you.
I’ve recently bought a LR77 v2 with WiFi option. My problem is that the router hangs very often. Several times a day. Lights are on – power and wan but no access to Internet or the admin web interface. Router is not reachable by ping. I’m running firmware 3.06 with factory defaults. Any idea why? Is it software or hardware error?
Thanks!
Erik
Jag utvärderade Conel LR77 som ett alterntiv för vanlig kontors-IT, men den höll inte måttet. Jag ville framförallt ha den för en kund som arbetar mycket i terminalserver.
WiFi-funktionen testade jag ganska lite, men jag hade också problem med den.
Conel verkar komma från Machine-to-machine-kommunikation, och där är tillgängligheten över tid viktigast. Om kommunikationen ligger nere någon sekund då och då är det ingen fara.
Men för kontors-IT (framförallt terminalserver) så är 10 st korta avbrott per dag inte acceptabelt.
Så vi strök den från vår lista. Detta var i augsti 2011, så saker kan ha ändrats sedan dess..
Hi, to be transparent, I represent Induo and we are the Swedish distributor for Conel.
@Erik I should recommend updating to the latest firmware 3.08 to solve these problems.
@Kalle If you tested in august 2011 it must be an early version of the LR77 router. A new firmware should fix these issues.
@Anyone, if you encounter problems with LR77 or any other router from Conel, please let us know by filling out our support form: http://www.induowireless.com/support/
Our aim is to provide reliable communications and by letting us know if you encounter problems with hardware we can more easily reach that goal.
@Ulf: Kul att höra. Jag ska omedelbart uppgradera en av mina routrar och testa.
@Kalle Bra, meddela mig gärna ditt resultat, jag bevakar inte denna tråd löpande så droppa gärna ett mail på ulf [kanelbulle] induo.com också, tack!